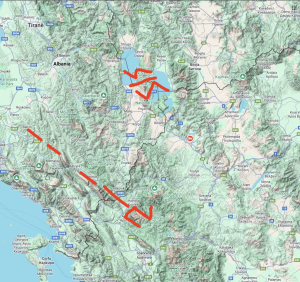
Beyond Proto-Writing: Reinterpreting the Dispilio Tablet as a Prehistoric Map for Optimal Pathfinding
by Peter MavronicAbstract The Dispilio Tablet, discovered in a Neolithic lakeside settlement in Northern Greece, is a wooden artifact bearing incised markings. Traditionally, research has